Invoking an Identity Service
The following are the methods you can use for an identity service.
- Login with provider type as Basic
- Login with provider type as OAuth/SAML
- Login with provider type as OAuth 2.0 with Deep link URL
- Get Backend Token
- User Profile
- Get Provider Name
- Get Provider Type
- Use Persisted Login
- Logout
Login with provider type as Basic
// Sample code to authenticate to Kony Fabric client var serviceName = "identity_service_name";
// Get an instance of SDK var client = kony.sdk.getCurrentInstance(); var identitySvc = client.getIdentityService(serviceName); var options = {}; options["userid"] = "userid"; options["password"] = "password"; // Optional values for login options["loginOptions"]["include_profile"] = false; options["loginOptions"]["isSSOEnabled"] = false; options["loginOptions"]["continueOnRefreshError"] = false; //Throws error if previous IdentitySession has expired options["loginOptions"]["persistLoginResponse"] = false; options["loginOptions"]["isOfflineEnabled"] = false; identitySvc.login(options, function(response) { kony.print("Login Success: " + JSON.stringify(response)); }, function(error) { kony.print("Login Failure: " + JSON.stringify(error)); });
- The isSSOEnabled flag set to true, indicating that Single Sign-On (SSO) is enabled. This parameter must be passed every time the user logs in. The parameters userid and password are required only for the first login. For more information about SSO, refer to Single Sign-On.
Supported Platforms for SSO Platform SDK Version Android 7.3 and higher versions iOS 7.3 and higher versions Web V8 SP4 and higher versions Support for Multi-Login with SSO is available from V8 SP4 and higher versions.
- The earlier code sample provides the following information:
- The include_profile parameter is set to true. This parameter specifies whether to encode the user profile as part of the claims token.
- The continueOnRefreshError flag is set to false. The default value is true. If the continueOnRefreshError is set to false and the previous identity provider session has expired, error 1017 is thrown. The error message is "Transient Login failed. Previous Identity Token expired in backend."
- From version 7.2.5 onward Kony Fabric apps allow users to use services protected by different Identity services in the same application session as long as users have authenticated to the Identity service. This allows a user to login to Google and Facebook, for example, via identity services and use integration services dependent on those identity services in the same application session, without having to logout of either.
- The isOfflineEnabled flag is set to true. The default value is false. This option allows users to use previous login information when they are in offline mode. Typically the login details are lost when the app is in offline mode. This option stores the user ID and password to be used if authentication is needed when there is no network connection.
To use the isOfflineEnabled option, you must enable the "Bundle OpenSSL Library" option in Project Settings. For information about this setting see Additional Settings.
This option is valid for iOS and Android platforms only.
This option is available for basic login only. It is not available for OAuth/SAML login. - The persistLoginResponse flag is set to true. The default value is false. This option allows users to login to an app once and reuse the response across multiple app sessions. Typically the login details are lost when the app is closed. The persistLoginResponse option stores the claims token in the data store of the client device. This allows the app developer to use the token to invoke the integration or object services without prompting the user to authenticate again. If the token has expired, the login will fail.
To use this option, the Kony Fabric server must be configured so that the Identity session is enabled for the entire time the persisted response is needed. For more information about configuration settings see How to Configure App Session Settings.
In the Android platform, you must also enable the "Bundle OpenSSL Library" option in Project Settings. For information about this setting see Additional Settings.
To retrieve the claims token from the data store, use the usePersistedLogin() API.
- When you select Kony User Repository as the identity type, the system does not allow you to provide an identity name.
- To use Kony User Repository as authentication service, the value for
providerNamemust be set asuserstore. If you set it with any other value (for example, Kony User Repository, User Store or Cloud Repository), the system throws an error.
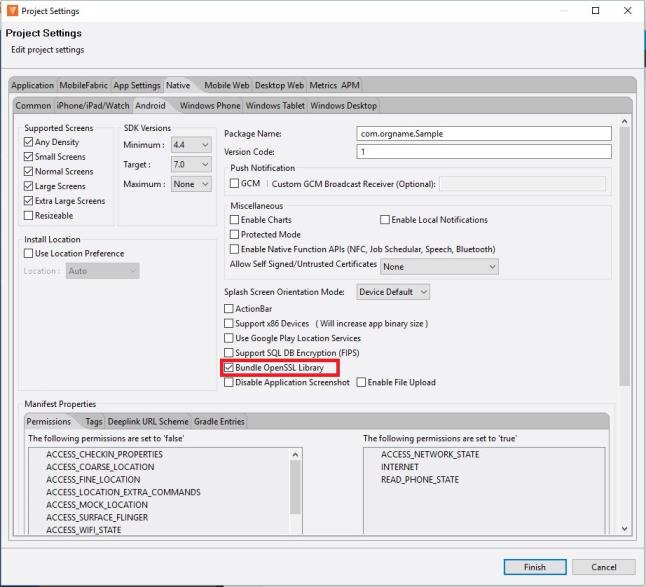
Additional Settings
To use the isOfflineEnabled and persistLoginResponse options in the Androd platform, you must ensure that the "Bundle Open SSL Library" option is enabled in the Kony Visualizer Project Settings. To do this, perform the following steps.
- On the File menu, click Settings to open the Project Settings dialog box.
- Click the Native tab.
- Click theAndroid sub-tab.
- Check the option for "Bundle OpenSSL Library".
The page will look like the following example.
Login with provider type as OAuth/SAML
// Sample code to authenticate to Kony Fabric Client var serviceName = "identity_service_name";
// Get an instance of SDK var client = kony.sdk.getCurrentInstance(); var identitySvc = client.getIdentityService(serviceName); var options = {}; options.include_profile = true;
//browserWidget is mandatory if using the MVC Architecture
options.browserWidget = myForm.myBrowserWidget;
var loginOptions = {}; loginOptions.isSSOEnabled = true; loginOptions.continueOnRefreshError = false; loginOptions.persistLoginResponse = true; options.loginOptions = loginOptions; identitySvc.login(options, function(response) { kony.print("Login success: " + JSON.stringify(response)); }, function(error) { kony.print("Login failure: " + JSON.stringify(error)); });
- The client is the kony.sdk(); object.
The earlier code provides the following information:
- The isSSOEnabled flag set to true, indicating that Single Sign-On (SSO) is enabled. This parameter must be passed every time the user logs in. For more information about SSO, refer to Single Sign-On.
- The include_profile parameter set to true. This parameter specifies whether to encode the user profile as part of the claims token.
- The continueOnRefreshError flag set to false. The default value is true. This flag throws error 1017 with error message "Transient Login failed, Previous Identity Token expired in backend". This error is thrown when the continueOnRefreshError is set to false and the previous identity provider session has expired.
From version 7.2.5 onward Kony Fabric apps allow users to use services protected by different Identity services in the same application session as long as users have authenticated to the Identity service. This allows a user to login to Google and Facebook, for example, via identity services and use integration services dependent on those identity services in the same application session, without having to logout of either. - The persistLoginResponse flag is set to true. The default value is false. This option allows users to login to an app once and reuse the response across multiple app sessions. Typically the login details are lost when the app is closed. The persistLoginResponse option stores the claims token in the data store of the client device. This allows the app developer to use the token to invoke the integration or object services without prompting the user to authenticate again. If the token has expired, the login will fail.
- When SSO is enabled, log out with SLO = true does not log out the OAuth provider.
To use this option, the Kony Fabric server must be configured so that the Identity session is enabled for the entire time the persisted response is needed. For more information about configuration settings see How to Configure App Session Settings.
For the Android platform, you must also enable the "Bundle OpenSSL Library" option in Project Settings. For information about this setting see Additional Settings. - To retrieve the claims token from the data store, use the usePersistedLogin() API.
From version 7.2.02 onward Kony Fabric SDK provides an option to customize the OAuth login form using a user-defined form with a browser widget inside it. The browserWidget parameter accepts a kony.ui.Browser instance. The SDK will run oAuth related logic on the provided browserWidget instance. This parameter enables a developer to provide a customized oAuth UI. If the provided value is not defined or if it is not an instance of the kony.ui.browserWidget, the SDK will create its own browser window with default configuration/customization for oAuth Login. - The browserWidget field is mandatory for Kony Applications built by using the MVC architecture on Kony Visualizer.
Login with provider type as OAuth 2.0 with Deep link URL
// Sample code to authenticate to Kony Fabric Client var serviceName = "identity_service_name";
// Get an instance of SDK var client = kony.sdk.getCurrentInstance(); var identitySvc = client.getIdentityService(serviceName); var username = "username_for_identity_service"; var password = "password_for_identity_service"; var options = {}; options["userid"] = username; options["password"] = password; options["UseDeviceBrowser"] = true; // This parameter in options will open the login url in native browser. // This is a deeplink url, where the control will be redirected after login. //#ifdef android options.success_url = "Deep link url registered for android"; //#else options.success_url = "Deep link url registered for rest"; //#endif identitySvc.login(options, function(response) { kony.print("Login success: " + JSON.stringify(response)); }, function(error) { kony.print("Login failure: " + JSON.stringify(error)); });
The sample above shows various parameters similar to the parameters of the Login with provider type as OAuth/SAML. The following two optional parameters are added further.
- UseDeviceBrowser: This parameter opens the login URL in the native internet browser of the device.
- success_url: After the log in is successful, control is redirected to the URL (deep link URL).
Deep link URL is the URL that is registered to the application. After redirection, the client calls the method handleDeeplinkCallback. (A global function)
Method signature: function handleDeeplinkCallback(query params)
// Sample code to call handleDeeplinkCallback after the deeplink redirection is done. // This method will be called after the deeplink redirection. //Need to register a call in the App services tab in App Events.function appservicereq(params) { handleDeeplinkCallback(params); // Required validations are done and proceed with rest of login flow. }
For more information on deep links, click here.
- The client is the kony.sdk(); object.
The earlier code sample provides the following information:
- The isSSOEnabled flag set to true, indicating that Single Sign-On (SSO) is enabled. This parameter must be passed every time the user logs in. For more information about SSO, refer to Single Sign-On.
- The include_profile parameter set to true. This parameter specifies whether to encode the user profile as part of the claims token.
- The continueOnRefreshError flag set to false. The default value is true. This flag throws error 1017 with error message "Transient Login failed, Previous Identity Token expired in backend". This error is thrown when the continueOnRefreshError is set to false and the previous identity provider session has expired.
From version 7.2.5 onward Kony Fabric apps allow users to use services protected by different Identity services in the same application session as long as users have authenticated to the Identity service. This allows a user to login to Google and Facebook, for example, via identity services and use integration services dependent on those identity services in the same application session, without having to logout of either. - The persistLoginResponse flag is set to true. The default value is false. This option allows users to login to an app once and reuse the response across multiple app sessions. Typically the login details are lost when the app is closed. The persistLoginResponse option stores the claims token in the data store of the client device. This allows the app developer to use the token to invoke the integration or object services without prompting the user to authenticate again. If the token has expired, the login will fail.
- When SSO is enabled, logging out with SLO = true does not log out the OAuth provider.
- The Deeplink API helps the device browser to authenticate the OAuth This can be used for any OAuth2.0 providers. If an OAuth provider does not allow embedded browsers, such as Google OAuth, you must use the Deeplink API, which launches the device browser instead of the embedded browser.
To use this option, the Kony Fabric server must be configured so that the Identity session is enabled for the entire time the persisted response is needed. For more information about configuration settings see How to Configure App Session Settings.
For the Android platform, you must also enable the "Bundle OpenSSL Library" option in Project Settings. For information about this setting see Additional Settings. - To retrieve the claims token from the data store, use the usePersistedLogin() API.
From version 7.2.02 onward Kony Fabric SDK provides an option to customize the OAuth login form using a user-defined form with a browser widget inside it. The browserWidget parameter accepts a kony.ui.Browser instance. The SDK will run oAuth related logic on the provided browserWidget instance. This parameter enables a developer to provide a customized oAuth UI. If the provided value is not defined or if it is not an instance of the kony.ui.browserWidget, the SDK will create its own browser window with default configuration/customization for oAuth Login.
Get Backend Token
// Sample code to get backend token for provider
var serviceName = "identity_service_name";
// Get an instance of SDK
var client = kony.sdk.getCurrentInstance();
var identitySvc = client.getIdentityService(serviceName);
var options = {
"requestParams": {
"refresh": "true"
}
};
var forceFromServer = false;
identitySvc.getBackendToken(forceFromServer, options, function(response) {
kony.print("Backend token is: " + JSON.stringify(response));
}, function(error) {
kony.print("Failed to get backend token: " + JSON.stringify(error));
});
- If forceFromServer is true, then the SDK fetches the token from the server. If forceFromServer is false, then the SDK gives you the token present in localStorage. Please note that only few backend providers such as Salesforce support refresh. If a backend provider does not support refresh, passing
forceRefreshFromServer=truewould result in empty response from this api. - The authClient is the IdentityService object.
User Profile
//Sample code to get user profile details var serviceName = "identity_service_name";
// Get an instance of SDK var client = kony.sdk.getCurrentInstance(); var identitySvc = client.getIdentityService(serviceName); var forceFromServer = false; identitySvc.getProfile(forceFromServer, function(response) { kony.print("User profile is: " + JSON.stringify(response)); }, function(error) { kony.print("Failed to fetch profile: " + JSON.stringify(error)); });
- If forceFromServer is true, then the SDK fetches the token from the server. If forceFromServer is false, then the SDK gives you the token present in localStorage.
- The authClient is the IdentityService object.
Get Provider Name
//Sample code to get provider name var providerName = authClient.getProviderName();
Note: The authClient is the IdentityService object.
Get Provider Type
// Sample code to get provider name var serviceName = "identity_service_name"; // Get an instance of SDK var client = kony.sdk.getCurrentInstance(); var identitySvc = client.getIdentityService(serviceName); var providerName = identitySvc.getProviderName();
Note: The authClient is the IdentityService object.
Use Persisted Login
When the login option (persistLoginResponse) is set as true, the auth response is stored in the datastore of the client device. You can invoke the usePersistedLogin API to check if the login response was stored.
If the API returns true, you can use the services authorized by that login without having to sign in again.
If the API returns false, you need to get authorized again. The persisted response is cleared only when you sign out.
Return Type: Boolean
// Sample code to retrieve the claims token from the data store. var serviceName = "identity_service_name"; // Get an instance of SDK var client = kony.sdk.getCurrentInstance(); var identitySvc = client.getIdentityService(serviceName); var isLoginPersisted = identitySvc.usePersistedLogin();
Logout
// Sample code to logout from auth service
var serviceName = "identity_service_name";
// Get an instance of SDK
var client = kony.sdk.getCurrentInstance();
var identitySvc = client.getIdentityService(serviceName);
var options = {};
options["slo"] = true;
options["browserWidget"] = myForm.browserWidget;
identitySvc.logout(function(response) {
kony.print("Logout success: " + JSON.stringify(response));
}, function(error) {
kony.print("Logout failure: " + JSON.stringify(error));
}, options);
- The authClient is the IdentityService object for the loggedIn provider.
- To log out from all applications, the user must log out of every Identity service that they are logged on to.
- The code sample shows the parameter slo set to true, indicating that all apps will be logged out when SSO is enabled.
- If slo is set to false, or if the app does not send slo, the user is logged out of the app. The user is not logged out of the other apps that are logged in using SSO.
- Any apps that use SSO based services must log in by entering credentials and re-initiating SSO.
For more information, refer to Single Sign-On.
| Copyright © 2020 Kony, Inc. All rights reserved. |
